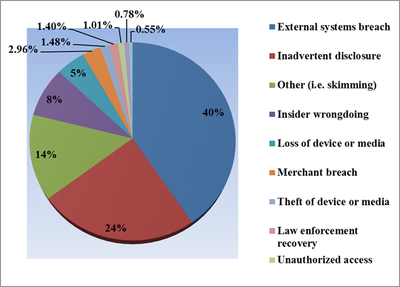
We are often asked about what measures our partner businesses should be taking to keep their information secure. Recently the office of New York State Attorney General Eric T. Schneiderman released a summary of the year 2016 data breaches, which were up 60% on last year. Unsurprisingly, hacking accounted for 40% of the incidents reported, but most worryingly employee negligence, including inadvertent exposure and device loss, was close behind at 37%.
If these findings from New York are in any way representative it seems that we need to take some active steps towards keeping our personal and business information safe.
Here are 6 simple steps that you can follow to keep your information as secure as possible:
1. Be vigilant with password management
We’ve recently re-evaluated our policy on passwords and here are some of the procedures we have been prioritising.
Arguably, more complex passwords are only marginally more secure. If you’re a normal person with a normal job, i.e. you don’t work for the government or on secret projects with incredibly high value, you are much more likely to be caught up in a bigger hack of a software you use than someone targeting you specifically. If this is the case then the steps below should apply to you.
- Use a different password for each login or system:
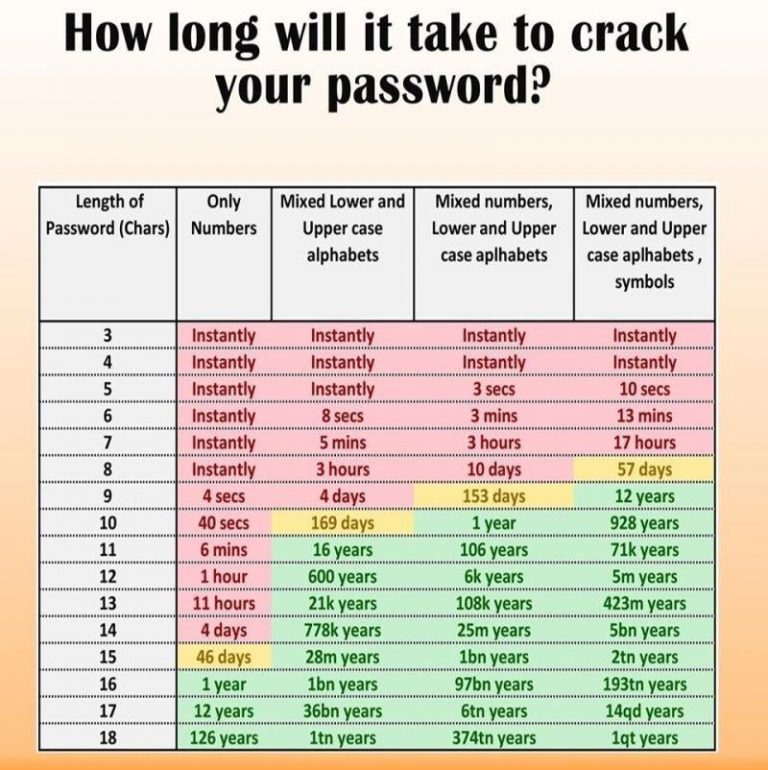
Due to an increase in computing power the type of attacks that are most common will happen whether you have a long or short password. This is because hackers use computers to quickly try multiple combinations.
It is obvious that if one of the many systems you use is hacked through no fault of your own, they now have the password that you use for every system. However, the scary thing is that the person who susses your password might not be the person that uses it. Passwords are often shared online so many other hackers can try them out. Thus, a different password for each of your logins, even if it is a simple one, will keep you more secure.
- Use a password management system:
The clever way to manage different passwords for everything is to use a password management systems. Think of these tools as a digital safe where only you have the correct credentials to open/decrypt them. Having done some research on the topic we have chosen to use 1Password. There are many that offer similar functionality but my personal choice was 1password as it is cross-platform, meaning I can use it for my personal and business login credentials without mixing them up – and across all of my devices.

- Go old school!:
Perhaps a little contentious but if you don’t have a password management tool, I would argue you would be better off using a different password for each system and writing it on a piece of paper and storing it somewhere safe. This is better than using the same long password for each system.
Finally, if you’re on a Mac don’t just rely on Keychain. It is useful but a couple of us have relied solely on it in the past and it can hurt!
2. Backup your data
There are many tools to help you with this, including those built into an operating system. All you need is an external hard drive which you can of course pick up very easily. Usually it is a 2/3 step process and you’ll be set up. Here are some useful links:
To backup/restore your Mac:
https://support.apple.com/en-gb/HT201250
To backup/restore your PC:
https://support.microsoft.com/en-gb/help/17127/windows-back-up-restore
There are also 3rd party services such as CrashPlan. These services will provide a similar offering as the native back up described above, but will also allow you to back up to another machine you might have or a cloud service.
3. Always keep your software up to date
Nice and simple to do these days as you get prompted to perform updates but it is very important to do so whenever it is offered.
4. Beware of suspicious email
Always have your eye peeled for suspicious emails. Here are a few things to look out for:
- Be careful before opening a link.
- If you feel an email is not legitimate check the email FROM address. Don’t reply to the name as it can hide the email, make sure you check the actual FROM address.
- If it isn’t from the domain of the provider, it is not legit. They can be quite sneaky. E.g. noreply@dhl.something.com
- To be legitimate it must be the company name next to the extension (.com) at the end. The example above is not and is likely to be something untoward.
- Where DHL is in the address as a subdomain, all this means is it is part of the domain to the right of it, in this case something.com. The domain is the most important thing and should be the same as the branding of the email you receive. If not then consider it to be spam or suspicious.
- An example of a legitimate email would be e.g. noreply@mail.dhl.com
- It is common of companies to use a subdomain (e.g. mail.) to send out email. If the main domain is as you expect (e.g. dhl.com) you are more than likely to be safe.
However, we should add the caveat that this does not cover the scenario where someone has gained access to the real email address to send out sinister emails. There is little you can do to catch these, they are rare and you just have to be sensible and don’t hand over information if you are ever unsure. Anything that asks you to enter a password should make you extremely wary. Never enter a password when you’ve followed a link from an email – even if the web site looks exactly like it always does – start from scratch to ensure you are going onto the real site.
Below is an excellent link from stay safe online.
https://staysafeonline.org/stay-safe-online/keep-a-clean-machine/spam-and-phishing
5. Set up multi authentication
This is where the a login system uses a second method to double check the fact that you are who you say your are. Banks have been doing it for a long time with card readers and more recently HMRC have added it to their processes. Many business tools offer it now but it’s usually up to you to activate the service. Here is where to head to set this up for some of the most common tools and sites that you might be using for your business:
Google has an authenticator app to help sites offer the service. This is already being used by Zendesk (a market leading ticketing software) and Xero. Our recommendation would be to accept this option if it is offered. As an end user, with certain services, you won’t get a choice as it will be a compulsory but do accept it if it’s optional.
6. Store your data very carefully
The steps above are all relatively simple and quick wins to keep things more secure. How you manage and store your data is crucial and needs ongoing concentration and careful processes.
From a business point of view this is one of your high-risk areas. The problems here are twofold. Firstly, much of the information you have in your care you are required by law to keep protected. Secondly, much of this information is essential to the smooth running of your business. Fail to protect it and your business is at risk.
From a process point even the smallest things can cause you an issue when it come to handling data. For example who has the latest copy of a document and where is it saved? Multiple copies of one document held by multiple people is so common and with this the security risk increases.
- Use a digital filing system
At a bare minimum it is worth considering having a digital filling system (an agreed way in your business to store information) but beware that you could still be exposed if you don’t know who has access, has taken a copy or has made changes.
-
- Even if your data isn’t at risk the efficiency saving of not having your team waste time searching for information or working on the wrong data can be enormous
- Consider converting to a system (bespoke or off-the-shelf) which can help centralise this information to minimise risk. The benefits of a system are:
-
- It can be set to encrypt all data.
- The access to data can be managed via the login. This means you know who can read and who can read/write.
- Information should be stored centrally on a server, whether in the cloud or in a server room. You don’t want the only copy on a laptop because something could happen to that laptop.
- Even if your data isn’t at risk the efficiency saving of not having your team waste time searching for information or working on the wrong data can be enormous.
And remember, data responsibility is key. You may be in charge of your client’s information? This is a big and very important subject. Managing this well and safely is very hard in a purely spreadsheet world.
It should be every company’s responsibility to make sure that:
“only authorised people can access, alter, disclose or destroy personal data and those people only act within the scope of their authority. If personal data is accidentally lost, altered or destroyed, it can be recovered to prevent any damage or distress to the individuals concerned.”
You can find out more information about the Data Protection Act on this link:
https://ico.org.uk/for-organisations/guide-to-data-protection/principle-7-security/
At home the situation is not hugely dissimilar, particularly because more and more services are opting for a paperless approach. You shouldn’t rely on their systems to store your documents. Ensure you download and keep your own copies.
To keep track, and therefore be as secure as possible, it can help to have access to the information from anywhere. Consider storing in tools like Dropbox, Google Drive, Box or iCloud. This will allow you to access information when you need it – wherever you are.